Cybersecurity User Personas
✨
Cybersecurity User Personas ✨
UX Research & Strategy Case Study
Understanding “Protector” Personas for Enhanced Alignment Around Users

🔎 Research Categories: Generative
📝 Project Type: Research-Backed User Personas
🕵️♀️ Role/Contribution: Research Lead, UX Writer, UX Strategist, Visual Designer, Illustrator
🗓️ Timeline: 6 months
🛠️ Relevant Tools: UserTesting, FigJam, Illustrator
🤝 Cross-Functional Team: UX Researcher, UX Manager, UX Designers
👥 Stakeholder Teams: UX, Product, Engineering, Support, Sales, Deployment, Product Marketing, Marketing
🔒 Users: 200 internal users (all employees and teams)
🎯 Business Outcomes:
Increase conversion rates of prospects to customers by equipping the sales team with further information about the prospective customers and what they care most about
Reduce overall resolution time for customer success and customer service calls by providing persona-based training materials to customer success/service team members
Strengthen strategic business decision-making by improving cross-functional alignment across previously siloed departments
🥅 High-Level Research Objectives:
Gain clarity on the various types of cybersecurity roles and their distinctions across different market sizes
Uncover the responsibilities and pain points of cybersecurity professionals
Study the tools utilized by cybersecurity professionals to fulfill their objectives
Jump to…
Project Context
Problem Statement
We aim to gain deeper insights into the needs and motivations of professionals who make cybersecurity decisions for their company to identify opportunities for enhancing our existing products, thus better serving them and alleviating their pain points.
Hypothesis
Through insights from our Marketing team's Buyer personas and data from our Sales team, the hypothesis is that the Protector personas will break down predictably based on market size.
Research Goals
Learn about what most troubles cybersecurity professionals and identify the root causes of these concerns.
Examine the distinguishing characteristics among different Protector personas and explore the factors that contribute to their differences.
Discover which security tools are the most important to Protectors and why.
Protector Personas
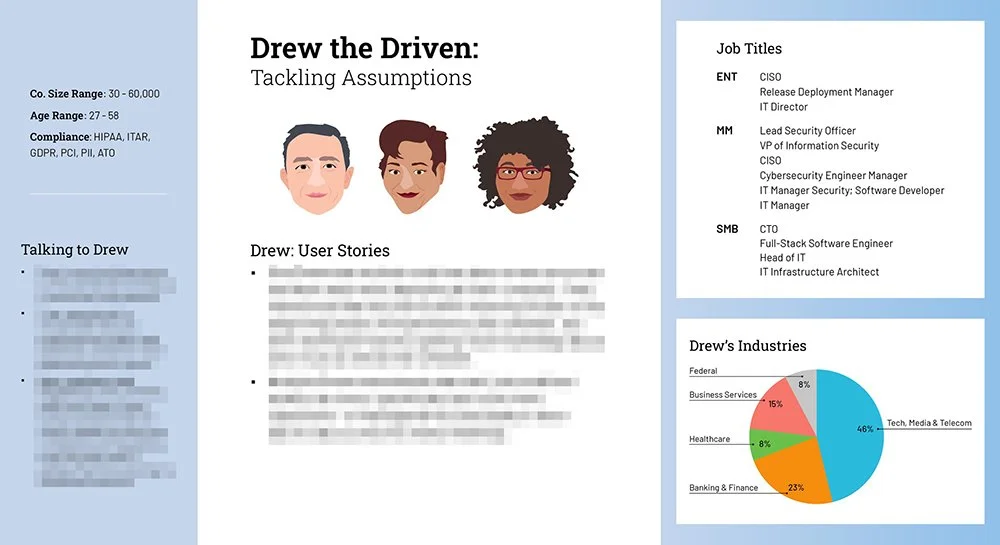
Drew the Driven
Drew represents a user with a medium level of cybersecurity knowledge and a high level of technology knowledge; they recognize that they still have much to learn when it comes to security. Drew may transform into an Andy later on in their career as they learn and gain more experience in security.
Mix of technical and operational responsibilities
High technical know-how
Medium confidence in their security knowledge
Feelings: Stressed, Satisfied, Frustrated, Bored, Challenged
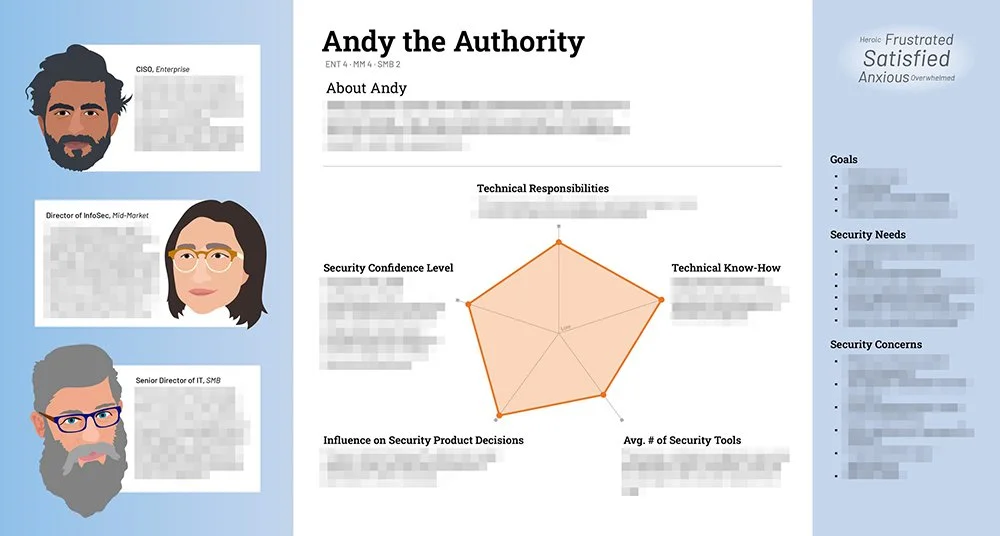
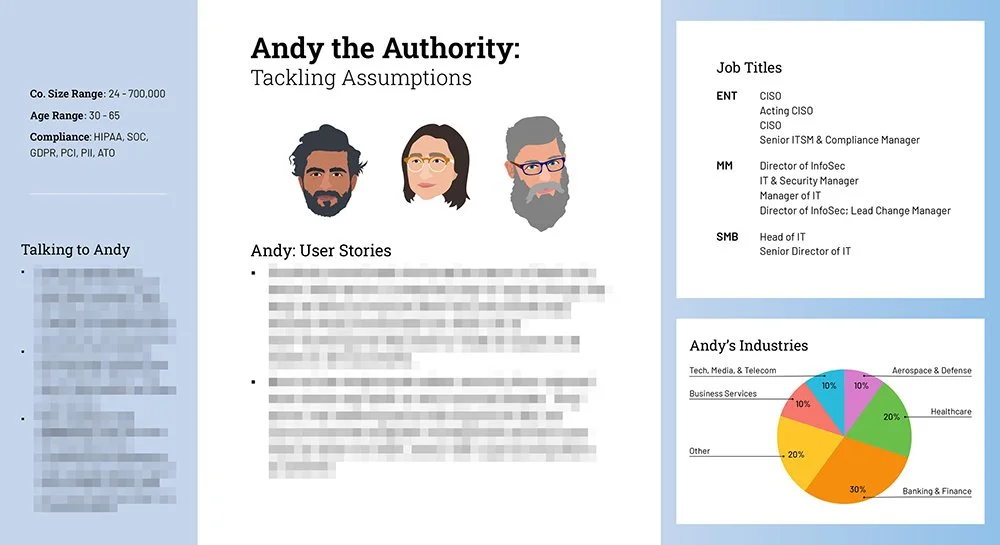
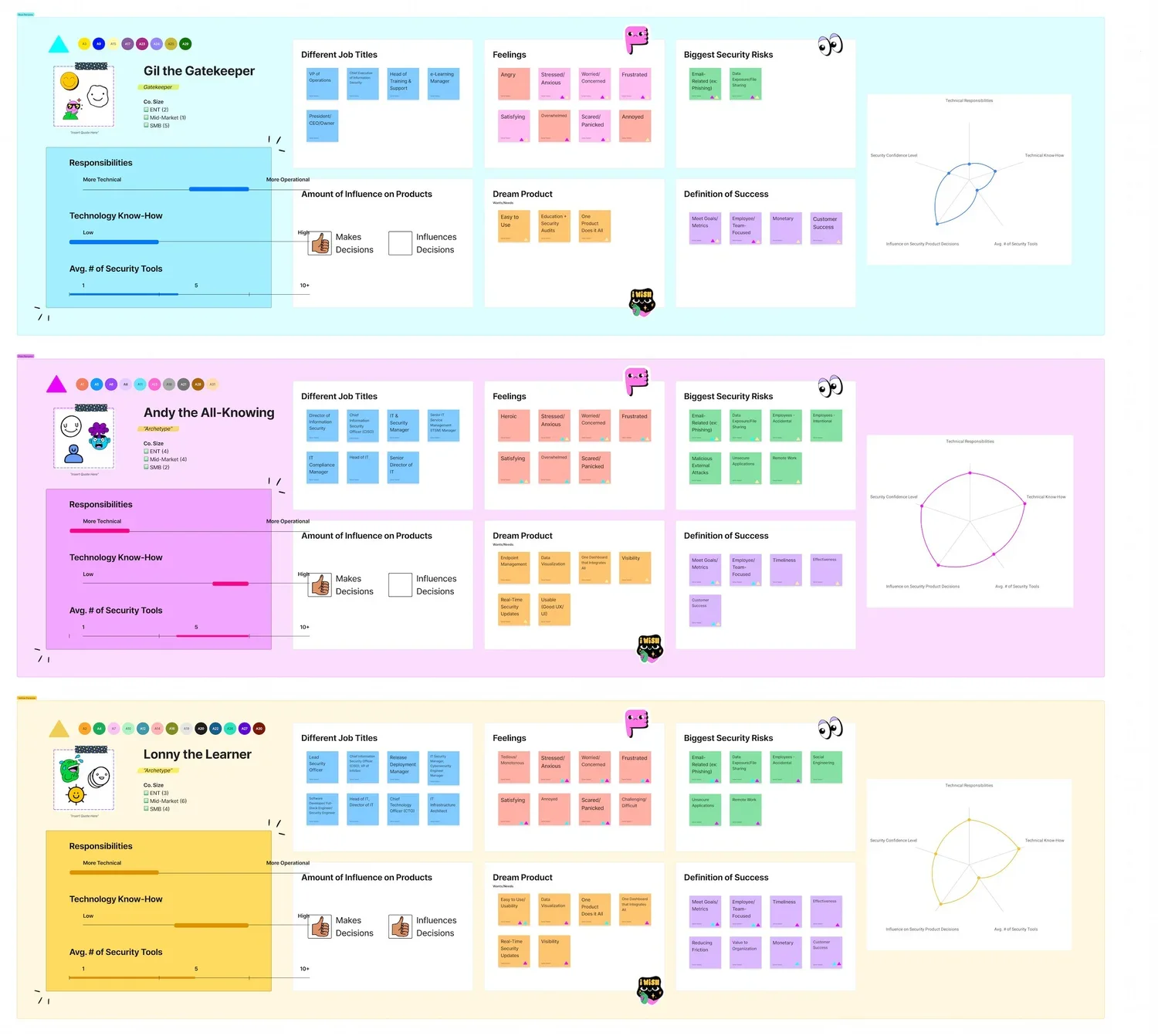
Andy the Authority
Andy represents a user with a deep understanding of cybersecurity and technology. They have a long history working in information security and stay informed of new trends in the field, including new products and new weak points.
Responsibilities are more technical than operational
High technical know-how
High confidence in their security knowledge
Feelings: Satisfied, Frustrated, Anxious, Overwhelmed, Heroic

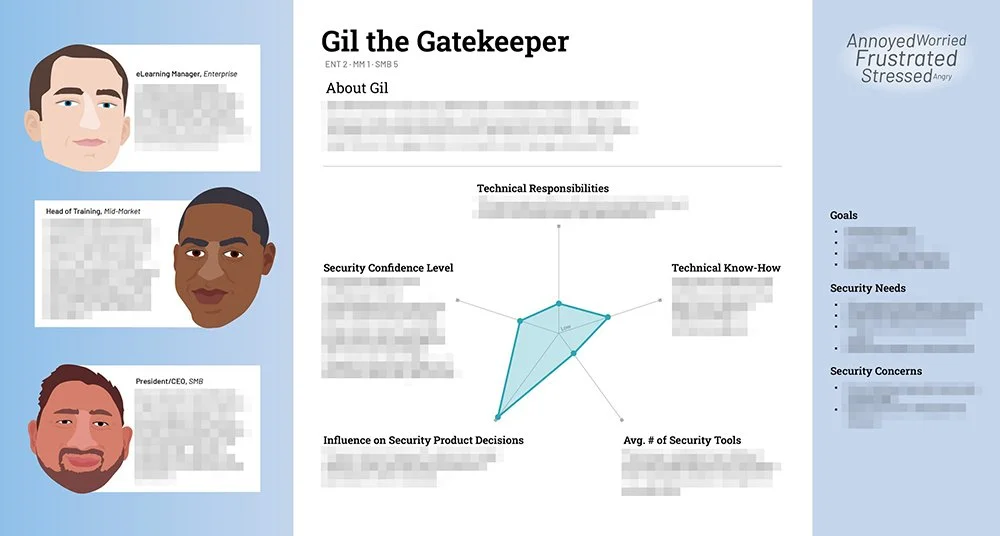

Gil the Gatekeeper
Gil represents a user in an executive or managerial role who does not have a strong understanding of cybersecurity as a field, despite making security product decisions. They know the basics but their background is operations-focused. They need help filling in the gaps when it comes to technology and security.
Responsibilities are more operational than technical
Low technical know-how
Low to medium confidence in their security knowledge
Feelings: Frustrated, Annoyed, Stressed, Worried, Angry
Actionable Insights
-
Traditional market segmentation by company size or industry missed what actually drives behavior: whether users see security as their primary identity (Andy), a stepping stone (Drew), or an inherited burden (Gil). Product marketing, onboarding flows, and educational content should speak to these distinct motivations—Andys need depth and credibility, Drews need clear paths to advancement, and Gils need simplification and reassurance.
-
Users' confidence levels don't always align with their actual expertise due to the Dunning-Kruger effect. Rather than assuming all admins need the same level of support, create graduated pathways: quick-win templates for overwhelmed Gils, advanced technical documentation for authority-seeking Andys, and career-building resources for ambitious Drews. This prevents both under-serving experts and overwhelming novices.
-
The diversity within each persona revealed that a one-size-fits-all value proposition wouldn't work. Product messaging needed to simultaneously communicate "enterprise-grade security" (for Andys who need to trust the tool) and "easy to implement and manage" (for Gils who feel overwhelmed). This insight directly informed the product roadmap and marketing strategy.
Business Impact
Research-backed personas enabled the company to segment and target customers more effectively, directly informing its go-to-market strategy and product positioning, which increased conversion and retention.
By moving beyond traditional firmographic segmentation (company size, industry) to behavior and motivation-based personas, we equipped Sales, Marketing, and Product teams with a shared language for understanding customers. This enabled more targeted messaging in sales conversations, more relevant content in marketing campaigns, and clearer prioritization in product development. The personas became foundational assets referenced across teams, leading to more strategic resource allocation and helping justify product roadmap decisions based on actual user needs rather than assumptions.
Research Impact
Strategic Impact
Personas shifted our product strategy from one-size-fits-all to differentiated experiences that served both security experts and reluctant administrators.
Prior to this research, product decisions were made with a vague "admin user" in mind, which often resulted in features that were either too complex for non-technical users or too simplistic for security professionals. The three distinct personas (Andy the Authority, Drew the Driven, Gil the Gatekeeper) revealed fundamentally different relationships with security responsibility, which informed strategic decisions about tiered deployment flows, educational content depth, and UI complexity. This insight was particularly valuable for the information architecture project that followed, where we designed navigation paths optimized for different user sophistication levels.
Update: This project was completed in late 2022. I left the company in late 2023. Years later, an Engineering Manager confirmed they still reference the personas across all departments. Huge win!
User Impact
Users experienced more relevant, contextual guidance that respected their expertise level and role relationship with security, reducing frustration for novices while maintaining credibility with experts.
Instead of overwhelming Gil the Gatekeeper with advanced technical documentation or boring Andy the Authority with oversimplified tutorials, users encountered product experiences calibrated to their needs. This meant Gils could accomplish security tasks without feeling incompetent, Drews could find resources to advance their careers, and Andys could access the technical depth they needed to trust the platform. The personas also influenced how Customer Success and Support teams approached different user types, leading to more effective and empathetic customer interactions.

Key Methodologies
-
Our initial hypothesis assumed security professionals would segment by company size, so I planned for 30 interviews distributed evenly across enterprise, mid-market, and small business (10 each). I completed 31 interviews recruited through UserTesting.
Because our target audience (security professionals) was niche, we iterated on our screener multiple times to ensure we were reaching the right participants: those with actual security decision-making responsibilities rather than just IT admin roles.
-
To move beyond our size-based hypothesis and discover what actually differentiated users, I applied segmentation analysis techniques from my NNG training. I created a matrix with each interviewee as a row and various attributes as columns (Feelings, Responsibilities, Industry, Technical Know-how, Tools Used, etc.). This allowed me to see patterns across dimensions we hadn't initially considered, revealing that factors like relationship to security responsibility mattered more than company size.
-
Once I identified promising attributes, I used dimension analysis to visualize clustering patterns. For each attribute, I created either categorical dimensions (discrete categories like "Satisfied," "Overwhelmed," "Confident" for Feelings) or continuum dimensions (sliding scales like "Operational ←→ Technical" for Responsibilities). Plotting all 31 interviewees across these dimensions revealed three distinct clusters that became our persona framework—groupings that cut across company sizes but showed consistent behavioral and attitudinal patterns.
-
Before jumping into polished persona cards, I created "skeleton" versions in FigJam to synthesize what made each cluster distinct. You can think of this almost like “wireframing” of the Persona Cards.
This intermediate step was crucial as it let me see each persona holistically and stress-test whether the differences between them were meaningful enough to warrant separate personas. It also helped me identify gaps where I needed to revisit the data or validate assumptions before committing to a final framework.
-
Understanding who our users were wasn't enough. We needed to understand what they were trying to accomplish. I collaborated with the product team to map specific Jobs-to-be-Done for each persona, identifying their functional, emotional, and social objectives when managing cybersecurity. This translation from persona characteristics to actual jobs gave product and design teams concrete, actionable direction for feature prioritization and development decisions.
-
To maximize adoption and minimize bias, I designed each persona as a two-card system: one with persona details and one addressing (and often debunking) assumptions from our original hypothesis and stakeholder interviews.
Critically, I created three different illustrations per persona to reinforce that these represent categories of users, not individual people. This approach enhanced empathy while preventing teams from over-indexing on superficial demographic details or treating personas as caricatures.
“As a marketing writer, I personally benefitted from Sahar’s audience personas that she developed from in-depth interviews with tens of clients. I refer to them for my content creation for the business on almost a weekly basis.”
“Will I be able to tell which persona I am? [reviews next slide] I think I’m an Andy!”
Reflections & Learnings
-
Sustained stakeholder engagement requires bringing people into the process, not just presenting polished outputs.
A 6-9 month research project risks losing buy-in if stakeholders only see results at the end. I combated this by running "Synthesis Jams" throughout the project, inviting cross-functional partners to participate in analysis sessions and see patterns emerge in real-time. This transformed stakeholders from passive recipients of research into active collaborators who felt ownership over the insights. The result? When it came time to implement persona-driven changes, teams were already bought in because they'd been part of the journey.
-
Creative dissemination strategies extend research impact beyond the initial presentation.
The comprehensive persona deck was information-dense by necessity, which risked overwhelming teams or limiting long-term retention. To address this, I hosted "Ask Me Anything" sessions where I role-played as each Protector (Andy, Drew, or Gil), letting stakeholders ask questions directly to the persona. This immersive approach made the personas memorable and helped teams internalize the differences between user types in a way that a slide deck never could.
-
Invest in rigorous research methods when the stakes warrant it, but know when lighter-weight approaches suffice.
Before starting this project, I completed Nielsen Norman Group's personas training to ensure I was using the most robust methodology available. The 6-9 month timeline and 31 interviews were justified because the Protectors were ambiguous, strategically critical, and would inform millions of dollars in product decisions.
However, for our Security Admin personas, we successfully relied on proto-personas (assumption-based frameworks) since that audience was better understood. This discernment – knowing when to go deep versus when to move fast – is essential for research leaders managing competing priorities and finite resources.
